Medium Demo
| To be better able to understand this demo, we strongly recommend you to read the simple demo first. This page demonstrates and explains the Shibboleth login procedure in greater detail and more technically than the simple demo. Should you prefer to get even more information about this topic, please read the expert demo. |
Overview
The demo scenario is the same as described in the simple
demo. A user wants to access a Shibboleth-enabled resource and has to be authenticated first.
For this demo, the following hosts are involved (as you will see from the URLs):
| Resource is on | https://aai-demo.switch.ch/secure/ |
| Discovery service is on | https://wayf-test.switch.ch |
| Home organization login is on | https://aai-demo-idp.switch.ch |
Phase 1 - User connects to Resource and is redirected
| To start the medium demonstration, try accessing the Shibboleth-protected demo resource. |
When you clicked on the 'demo resource' link the following two things could have happened.
- You were granted access to the resource directly:
Since you already had a valid Shibboleth session, you were granted access directly. This can be the case if you previously were authenticated. - You were redirected to the Discovery Service:
When you tried to access the demo resource, the web server on that host detected that you don't have an established Shibboleth session. Therefore, you were redirected to the SWITCH Discovery Service.
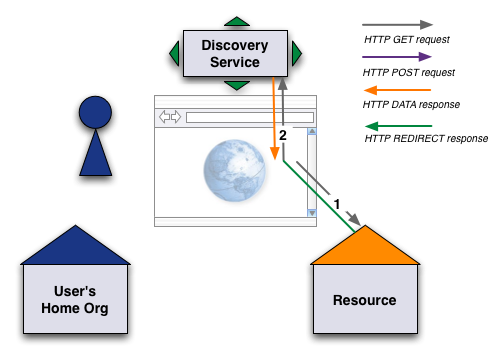
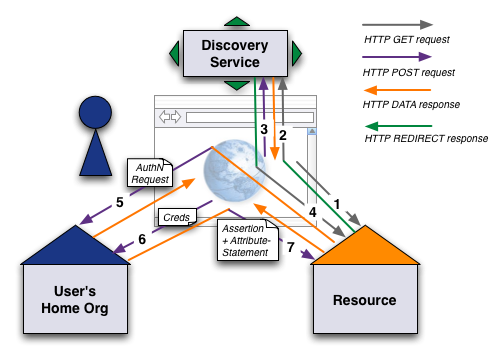
The following steps explain what actually happened in this phase.
- Step 1:
- When you clicked on the 'demo resource' link, your web browser sent an
HTTP request to 'aai-demo.switch.ch' for the webpage '/secure/'
The web server answered with an HTTP Redirect to the Discovery Service located at 'wayf-test.switch.ch' because you didn't have yet a valid Shibboleth session because you were not yet authenticated. - Step 2:
- After the redirect, the Discovery Service sends your web browser an HTML web page with the pop-up list with all Home Organizations that are available. In this demo, you will only see Home Organizations of our test infrastructure.
Phase 2 - Authentication Request
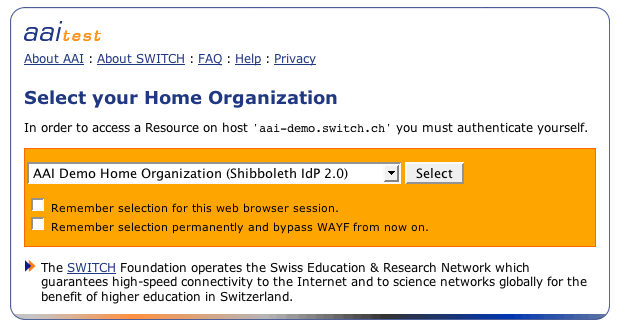
| Select 'AAI Demo Home Organization' as Home Organization for this demo and hit the 'Select' button. |
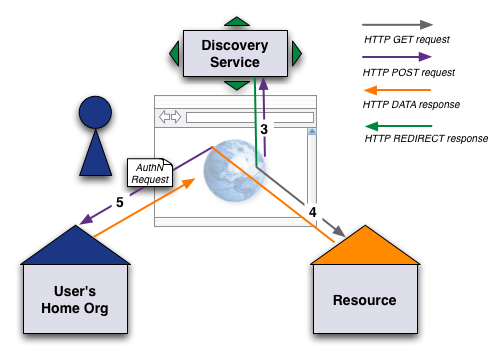
- Step 3:
-
The user submits the Home Organization selection form.
The Discovery Service answers with a redirect to the session initiator of the resource. - Step 4:
- The session initiator creates an authentication request for the choosen Home Organization and submits it through the users browser to the Home Organization.
- Step 5:
- The Home Organization evaluates the authentication request and answers with the login page.
Phase 3 - Authentication and Access
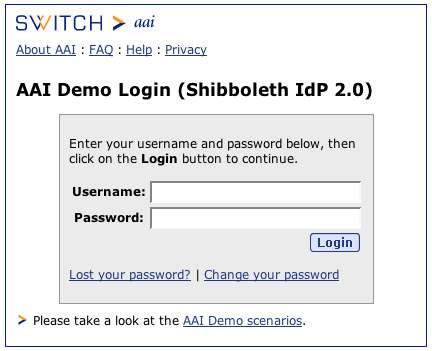
| Use the credentials 'demouser' as username and 'demo' as password. Then click on 'Log in'. |
If you selected another Home Organization than 'AAI Demo Home Organization', the login page will look different and is located on another server. In that case you have to provide the corresponding credentials for that Home Organization to successfully log in.
Besides the login name and password, other forms of credentials could be used. E.g. one could use biometric authentication methods or a chip card to authenticate, provided the Home Organization supports such advanced authentication methods.
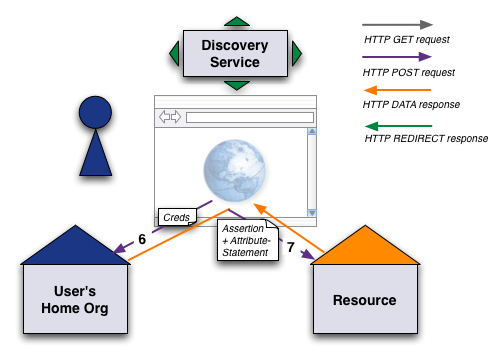
- Step 6:
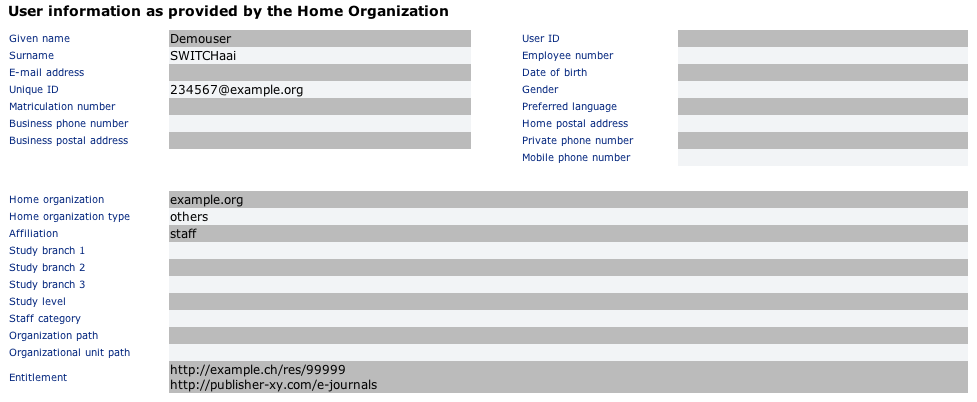
- The user provides his credentials to the Home Organization. The credentials are checked and an assertion including the users attributes is created according to the attribute filter rules.
- Step 7:
- The assertion then is submitted through the users browser back to the resource. Due to the user's attributes, the resource can perfom the authorization checks. If the authorization is successful, the user is redirected to the resource page that was initially requested.
Security Summary - Shibboleth Login Procedure
In Fig. 8 all involved connections are shown again. They all are secured with SSL and the user's attributes are also encryped when they are transported via the web browser. This makes sure, that neither the user or a malicious application on the user's computer has access to the attributes.
Besides the technical security measures there is also a legal basis that provides some security. All Home Organizations and their resources have agreed to the AAI Service Agreement, which guarantees confidential use of user data according to the Swiss data protection law.
Expert Demo
| Read the expert demo for even more detailed information about the login procedure. |