SAML 1 Attribute Push Relying Party
Note: This relying party is only used for SWITCHaai Federation Partners, namely publishers, whose SP is unable to use SAML2, despite the SAML2 protocol was introduced back in 2005!
The metadata files for the SWITCHaai and the AAI Test federations contain a special EntitiesDescriptor element that includes multiple EntityDescriptor elements. This EntitiesDescriptor represents a relying party that usually contains one or more Service Providers. The relying party's name (and thus also the EntitiesDescriptor's name) corresponds to the URL https://www.switch.ch/aai/SAML1/Attribute-Push, which points to this web page.
As the URL suggests, this so called "attribute push relying party" can be used together with the below configuration snippet to tell a SAML 1 Identity Provider to push the user's attributes to all Service Providers within this relying party as depicted in the orange box of the illustration.
So, there is no need for them to open a separate backchannel request anymore for a separate attribute request. Therefore, this is an alternative way of transmitting the attributes in comparison to the default SAML 1 attribute pull method (top illustration), where a Service Provider opens a SSL protected back channel connection to the Identity Provider to pull the attributes from.
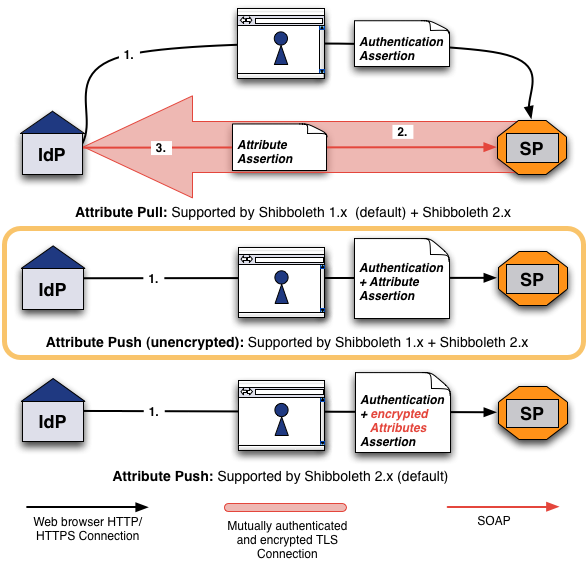
Attribute Push (the default method in SAML2) has the benefits of being more reliable, more compatible and faster. Provided the Service Provider's assertion consumer URL is accessed over https, the pushed attributes should be safe from third parties. However, in SAML1 (unlike in SAML2) it is not possible to encrypt the user's attributes. Therefore, malicous code on the user's computer as well as the user himself could in theory read the transmitted attributes. Therefore, the security and data privacy is lower than with attribute pull.
The use of this relying party thus is generally recommended only for Service Providers that request non-personal data like the affiliation, eduPersonEntitlement, Home Organization, Home Organization type.